In large-scale enterprise environments—spanning remote edge sites, data centers, and multiple clouds—manually managing data is a recipe for inconsistency and data loss. As the Founder and CTO of EnduraData, I’ve seen firsthand how automation via the Command Line Interface (CLI) is the only way to achieve true resilience at scale.
While a GUI is excellent for initial visualization, the CLI is the language of DevOps and high-availability systems. It supports headless operation on OpenBSD, Linux, and Windows, making it ideal for secure environments where a desktop is not an option.
1. The Anatomy of Automation: eddist.cfg
The heart of any EDpCloud deployment is the eddist.cfg file. This is where you define your topology: unidirectional, bidirectional, or multi-directional.
A common challenge I help our customers solve is the “Many-to-One” aggregation model used by large federal agencies like the Social Security Administration and Medicaid. By automating the configuration, we eliminate human error in complex multi-site environments.
- Deep Dive: For a complete breakdown of transmission parameters and security filters, consult the eddist.cfg technical guide.
2. Multi-Site Bidirectional Sync: A Real-World Code Example
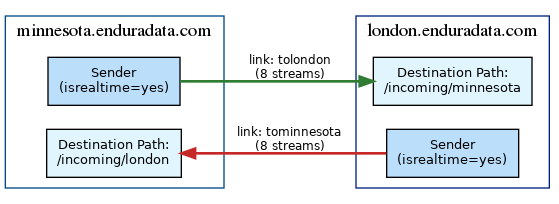
For many organizations, the goal is a “Follow-the-Sun” or “Active-Active” data model in which two sites (e.g., Minneapolis and London) remain perfectly in sync. Any change on one side is immediately reflected on the other.
Below is a technical example of how you would configure a bidirectional relationship between two nodes in eddist.cfg:
<?xml version="1.0" encoding="UTF-8"?>
<config name="enduradata" password="***************" workers="8">
<!-- Link 1: Minnesota to London -->
<link name="tolondon" deletes="no" >
<sender hostname="minnesota.example.com" isrealtime="yes" />
<receiver hostname="london.example.com" storepath="/incoming/minnesota" />
</link>
<!-- Link 2: London to Minnesota -->
<link name="tominnesota" >
<sender hostname="london.example.com" isrealtime="yes" />
<receiver hostname="minnesota.example.com" storepath="/incoming/london" />
</link>
</config>In this setup, we use the realtime type to ensure that file events are picked up as they happen, significantly reducing the Recovery Point Objective (RPO).
3. Managing High-Volume Ingestion with edstat, edjob
When you are replicating millions of files monthly—as many of our customers do—visibility into the replication queue is critical. If a network link goes down, data accumulates in the queue.
The edstat tool allows sysadmins to inspect these message queues without stopping the service. For example, to check the status of a specific queue, you would use:
edstat -l tolondon
edjob -l tolondon
- Technical Reference: Learn how to prioritize critical data over secondary logs by visiting the edmfq documentation.
4. Security & Resilience: Ransomware Tolerance
A core focus of our recent development has been Ransomware Tolerance. By utilizing the CLI to configure specific “Pull” replication or “No-Delete” policies, you can ensure that even if a source machine is compromised by encryption, the destination repository remains untouched.
This prevents an attacker from using the replication stream to delete your backups.
5. Real-Time Monitoring and Health Checks
Automation is only as good as its monitoring. Using status, you can pipe replication health directly into your existing monitoring tools like Nagios, Zabbix, or even custom OpenBSD scripts:
edstat| grep "xyz"
This allows your team to receive alerts before a minor delay becomes a major synchronization gap.
- Service Control: For managing the background processes, see the CLI tools.
- Monitoring Detail: Review the edfsmonitor configuration for fine-tuning file event triggers.
Conclusion
By leveraging the CLI, you move from simple file copying to sophisticated data orchestration. This level of control is why organizations have relied on the principles behind our distributed systems.
Share this Post