Why Managed File Transfer or MFT?
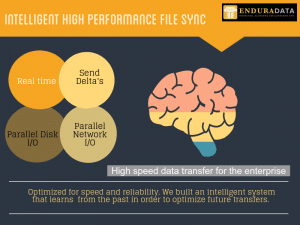
Intelligent, high-performance file sync.
Managed file transfer is an essential part of conducting business in every industry across the board. File sharing generally transpires by using File Transfer Protocol (FTP), email, or the internet, but the issue with those approaches is that they are not easily governed. Questions concerning the security of confidential files, who received them, and when are often asked. One way to confront any concerns an organization may have with the safety of their file sharing is to secure Managed File Transfer (MFT) [1].
What is Managed File Transfer?
Managed File Transfer is software that securely manages file sharing and transfer [1]. MFT software is intended to assist businesses with the growing compliance, security, and system requirements of distributing data [4]. It works by using a network to transfer files from one system to another. To securely transfer the file, security features, such as file encryption are added to maintain the privacy and integrity of the file. This hinders any hackers on the networks from gaining access to the file’s contents and changing them [5].
Since traditional data sharing methods such as File Transfer Protocol (FTP) and email are not easily controlled, MFT is a valuable tool because it helps organizations audit and track their file sharing and increases accountability amongst users. While the old standard, FTP, may use cloud services, it is not an adequate choice for businesses to use information safety and privacy concerns [1].
How does MFT work?
The method in which Managed File Transfer approaches data protection is by giving users control over their access. How access control is accomplished differs amongst secure file transfer products, but the basic concept is shared code between the source and the receiver. It could be as easy as an established passcode or as difficult as incorporating an identity and access management (IAM) system. The code is utilized to scramble the file before its transfer from the source to the receiver. Once the recipient obtains the encrypted data, the file is decrypted by their computer using the agreed-upon secret [5].
Benefits of MFT?
It has become crucial for organizations to have dependable file transfer solutions and tools available to assist them in preserving the security of their vital data whilst it is transported across various digital platforms. Due to its ability to do so, MFT is gaining popularity as a practical alternative to traditional file transfer solutions [5].
There are several reasons why the use of MFT is valuable to businesses. Such benefits include:
- It assists businesses to improve compliance, protection, and control involved in information transfer [2]
- It provides auditing capabilities that other secure file transfer systems do not possess [5]
- It has state-of-the-art technologies that provide automated storage and removal abilities from the depository to guarantee compliance with data preservation guidelines [5]
- It increases organizations’ capabilities and productivity [2]
- MFT has more vigorous scheduling abilities compared to its counterparts [5].
Why is MFT use growing?
MFT’s use is currently on the rise. As such, the marketplace of MFT is expected to increase at a compound annual growth rate of 10.2% by 2020 [2]. In fact, the marketplace should top $1.6 billion by 2024 [3].
There are multiple reasons why MFT use is a growing market in various industries. Industries have listed the following as reasons why MFT use is on the rise [3]:
- Increases in cyber crimes
- The upsurge of information production
- Rash of compliance guidelines
- Growing need for data control
- Increases of bring your own device (BYOD).
The following industries are expected to experience the biggest increase in MFT implementation due to data protection dangers and increasing compliance stipulations: healthcare, finance, and insurance [2].
What MFT services and features are available?
Before employing automated file transfer, businesses need to ask what kind of MFT service they want or need to use. The kinds of services are called deployment types. However, even before the organization can choose the appropriate deployment type, they must first ask themselves what safety features are required. The safety features offered are [1]:
- Encryption
- Safe HTTPS/FTP systems
- Automatic transfer
- MFT can also be used alongside FTP to help make it safe. Organizations can preset the MFT to block specific data or IP addresses, impose password guidelines and put transfer limitations on users.
Once the needed safety features are determined, organizations can choose the deployment type they wish to utilize. The following are the deployment types available [1]:
- Cloud-based [1]
- A good option because it’s low maintenance and inexpensive
- On-site software that is self-installed and controlled [1]
- It accounts for the prevailing type of deployment as of 2014, encompassing 59% of the total marketplace [3]
- On-site deployment is most desired by businesses that create large quantities of confidential information [3]
- Hybrid [1]
- A blend of cloud-based and on-site deployments [3].
Conclusion
File transfer methods provide organizations a simple method to transport files from one location to the next while protecting the information’s privacy, reliability, and accessibility. The various traditional systems are economical and have been commonly utilized for years, mostly for automatic transfers. Nonetheless, contingent on the type of information being shared, it may be best for businesses to use an MFT system due to its innovative protection, administrative, and auditing features [5].
Download EDpCloud and try it now.
References
- Rashid, Fahmida (4 September 2015). “The Best Secure Managed File Sharing Services.” PCMag. Retrieved 3 March 2017.
- “Managed File Transfer Market – Rising Trend in Application Integration & Cloud-Based Managed File Transfer Solutions.” PR Newswire. 23 February 2016. Retrieved 3 March 2017.
- “Managed File Transfer Market Expected to Reach US$ 1.6 Bn by 2024 Globally: Transparency Market Research”. PR Newswire. 26 May 2016. Retrieved 3 March 2017.
- Rouse, Margaret. “Managed file transfer (MFT).” WhatIs.com. Retrieved 2 March 2017.
- Scarfone, Karen (2015). “What to Look for in Secure File Transfer.” TechTarget. Retrieved 3 March 2017.
By Nicole P., EnduraData Communications
Related articles
https://www.enduradata.com/copy-data-management-cdm/
https://www.enduradata.com/file-sync-edpcloud-software/
https://www.enduradata.com/edpcloud-data-synchronization-software/
Share this Post